On September 5th I discovered a non-password protected database that contained 1 folder named “Customers”. Every file contained references to Verlo Mattress Factory and appeared to be customer data. Upon further investigation there were indications that this could be a franchise or a single location. The files referenced “Customers – VMFS of Greenfield” and according to Verlo’s website there is a store located in Greenfield, Wisconsin that is owned by FWR of Wisconsin LLC.
According to a press release from May, 2018:
Founded in 1958 Verlo Mattress is owned by Marcus Investments and Verlo Mattress’s Corporate office is located in Milwaukee (about 9 miles from Greenfield). This exposed database allowed anyone with an internet connection to see what type of data is being stored and collected in Verlo’s “ecosystem of technology”. According to the same press release there are 37 corporate and franchise locations.
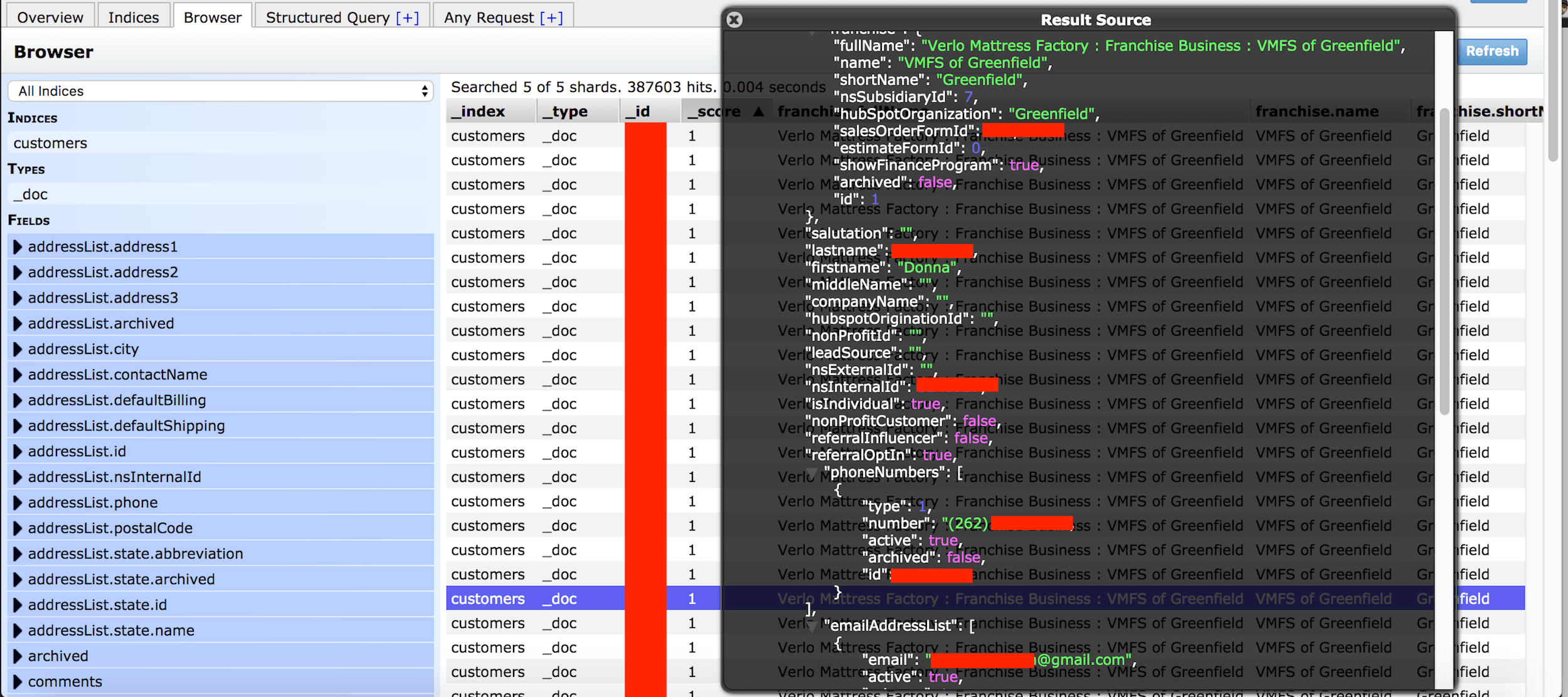
Here is what we have discovered:
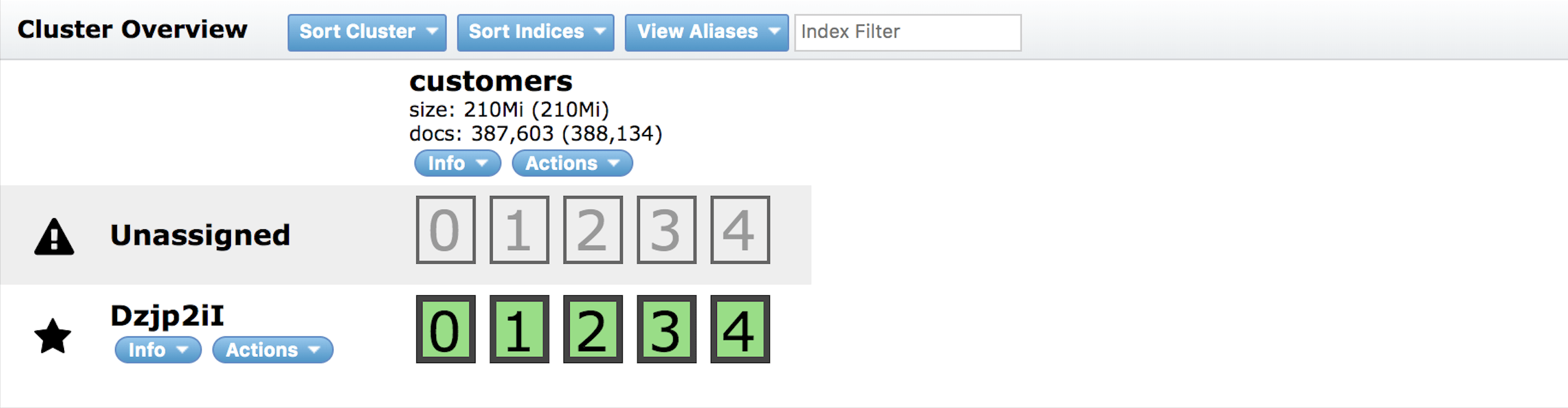
- This was an Elastic database set to open and visible in any browser (publicly accessible) and anyone could edit, download, or even delete data without administrative credentials.
- 387,604 records with names, phone numbers, emails, home address, billing address.
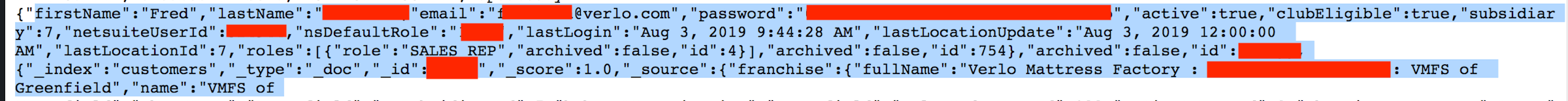
- Login credentials with hashed passwords for internal users
- IP addresses, Ports, Pathways, and storage info that cyber criminals could exploit to access deeper in to the network.
Despite multiple attempts for comment no one from the Verlo Mattress Company replied or acknowledged my messages. However, the database access was restricted soon after I sent the first notification. It would have been nice to know if this was indeed a single franchise dataset or more? who managed it? was it the corporate office or the franchise that was responsible?
When organizations go silent we can only guess or speculate the unanswered questions. In my professional experience the best thing anyone can do is be open, honest and transparent about any data incident. I am not implying that the Verlo Mattress Company or an individual franchise has done anything wrong and I understand that every organization has their own policies and procedures. In my experience companies and organizations are usually responsive and grateful to security researchers that identify vulnerabilities that could affect their business or customer data.
My advice to any company would be to have a Data Security Policy in place and include things like how to communicate with outside members of the security community if they contact you, eliminate the “Firewall” of getting a notification to the right person, establish how to structure a bug bounty program internally to encourage responsible disclosures of a data breaches, etc. We consult clients everyday on how to be prepared and follow best practices when it comes to data protection policies and I am passionate about this subject. In today’s world, it is not if a data breach will happen, it is a matter of when the data breach will happen. Being prepared means having a step by step plan to follow when an incident occurs and ensures effective communication with right person or team who can take action.
It is unclear how long the data was exposed or who else may have gained access to it before I responsibly disclosed my discovery to the Verlo Mattress Company. It is also unclear if the affected customers or the authorities were notified. Section 134.98 of the Wisconsin Statutes requires businesses to notify individuals if an unauthorized person has acquired their personal information. The business must be operating in Wisconsin and maintaining personal information about individuals who reside in Wisconsin. The law defines highly sensitive information as SSN, Credit Card or Banking data, Medical etc.
In this instance it appears that Verlo did the right thing by separating payment data or credit information and I did not see any evidence of payment details in the database. Technically as the law is written they were not required to report the incident. In the security world any exposure is still a potential backdoor that could allow cybercriminals to penetrate deeper inside the network.
Hypothetically, the real danger with this kind of data would have been if cybercriminals conducted a targeted phishing campaign to customers. If these customers are used to receiving offers and discounts from the organization it would theoretically be very easy for cyber criminals to “Spoof” the email address to appear that it came from the business they trust. What would be even worse is if Criminals call you on the phone number they got from the database and confirm your account number or other details in an attempt to get a credit card number. The size of Verlo’s database and knowing these were specific customers would have made this a gold mine for phishing. We have all received calls from fake tech support or fraudulent IRS agents, so this is not beyond the realm of possibilities when it comes to how creative criminals are these days.
*Please note* I am not indicating or implying that customers are at risk or that this will happen. I am only presenting a scenario or possibility as a reference of how this data could be abused by criminals. In conclusion, I am glad we were able to identify this vulnerability and we hope it helps them strengthen their data protection policies and procedures going forward. At the time of publication no statement has been given by Verlo Mattress Company and I will update the article in the event we are provided any statement or more details.