On December 1st 2018 Bob Diachenko found a misconfigured database that has publicly exposed millions of user contacts, SMS, and call records that appear to belong to Tri.co.id. With over 260 million total records this is a massive discovery, but what is worse is that the database is still unsecured and publicly accessible. Tri or “3” is a GSM (Global System for Mobile communications) operator and mobile internet service provider and is a division of Hong Kong-based multinational conglomerate CK Hutchison Holdings.
Language barrier and email security
We contacted them the same day as the discovery and followed up for 20 days since a data leak notification email was first sent. Multiple calls to their support went nowhere. Finding someone who could speak English was difficult and then they could not give us any additional contacts once we reached them. Jeremiah Fowler of SecurityDiscovery.com even reached out to their parent company CK Hutchison Holdings but discovered that their email security system rejects hyperlinks and attachments. Without proof they likely ignored the notices as just another SPAM message. In this case strong email security methods actually blocked the data leak notifications.
Type of breach:
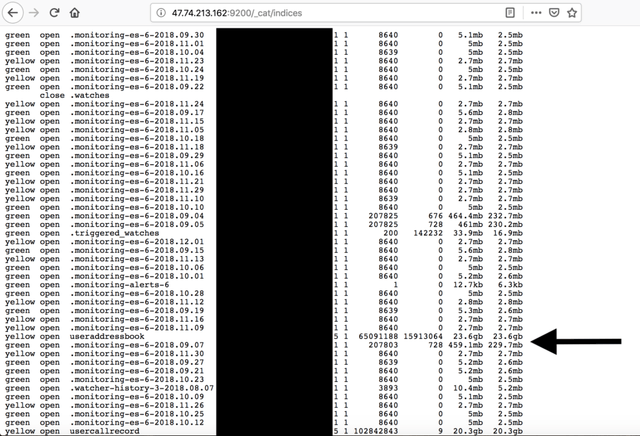
IP: An ElasticSearch incident was misconfigured to allow anyone access to millions of records with no password protection.
Type of data leaking:
- User SMS (91,395,499)
- User Contacts (65,089,606)
- User Call records (102,839,952)
One Month Later.
Usually we do not disclose or report on data breaches until they have been secured and sensitive data is no longer publicly accessible. After many attempts we had exhausted our notification process. Somehow by Jan 11th it seems that they finally got our messages or someone else alerted them to this massive exposure of their customers and the data is no longer accessible.
CK Hutchison Holdings provides mobile telecommunications services in Indonesia, Vietnam, Sri Lanka, Australia, Austria, Denmark, Hong Kong, Ireland, Italy, Macau, Sweden and the United Kingdom.
