Earlier this year, I discovered that SMS marketing firm, Rocket Text (rocket-text.com), failed to secure its Mongo database exposing just over 63 million customer emails and phone numbers.
Rocket Text, formerly known as ApexSMS, first came under scrutiny after a May 2019 disclosure by myself to TechCrunch highlighted that the company failed to secure its Mongo database of customer information by neglecting to password-protect their server. This lack of simple server protection is exactly the same kind of failure I would find again with the recent leak associated with Rocket Text.
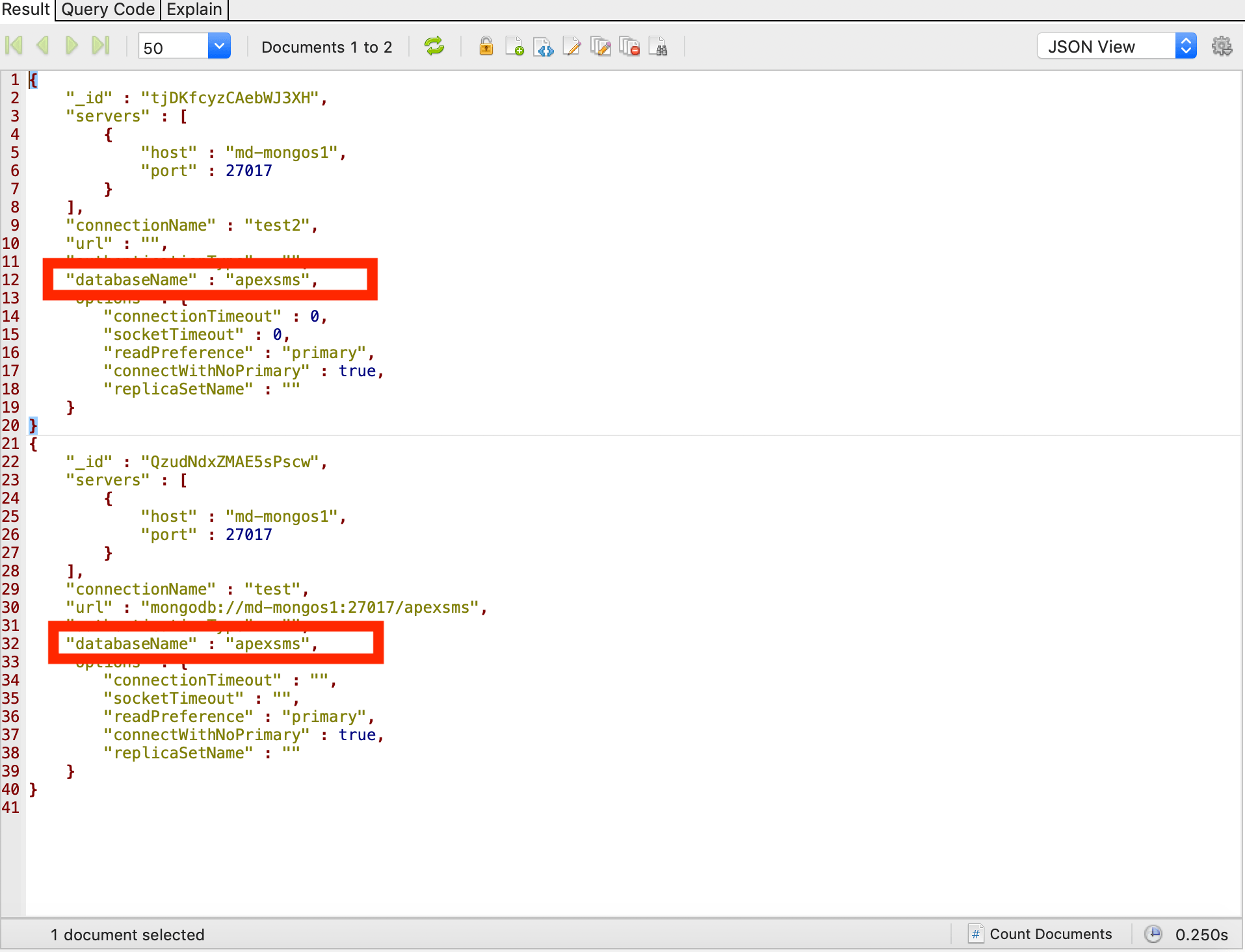
- I connected the dots between the two marketing firms by observing that the exposed Rocket Text database is set up in exactly the same manner as ApexSMS and also shares the same database administrator. Moreover, the below picture demonstrates that even the URL associated with the Mongo DB is named “apexsms”.
The exposed records include:
- First Name
- Last Name
- Email Address
- Postal Address
- Zip Code
- Phone Number
In the previous leak, there was a distinction made between cellphone numbers and landlines in the data. In this leak, however, that distinction is not made, but we assess that the numbers being leaked and unprotected on the server are cellphone numbers based on our technical analysis. We note that not all marketing firms are this careless with our data. Most companies go to great lengths to ensure that our personal information is protected commensurate with today’s high industry standards. Regardless, it is time for us to own our digital footprint by being mindful of what we click on, sign up for, and the terms of the offers associated with today’s miraculous technological advancements.
- Do not be afraid to unsubscribe from online services you no longer use
- Ask hard questions about a company’s security posture,
- And become aware of who knows what about you.
Interestingly, I reached out to the Rocket Text support team at the email address provided on their website, but the email was returned, and I was informed that the “…email account does not exist.”
“Smishing:” The Dangers of SMS Phishing and How to Avoid It
Major phone number leaks, like the one from Rocket Text, exposes clients to SMS phishing…also known as “smishing.” Mobile spam is not just annoying. It can be downright dangerous if it tricks you into clicking on a link that will inject malware into your system or that will steal your personal information.
Protecting Yourself from SMS Phishing and Mobile Text Spam
As more and more people make greater use of smartphones to manage their online banking and accounts, the risk from smishing becomes even greater. Here are a few tips to avoid falling prey to SMS phishing scams beyond simply avoiding clicking links in SMS messages:
- Always be cautious, even if you think you recognize a phone number. Remember that criminals will spoof numbers to make it appear that they are calling from trusted numbers.
- Don’t reply to a text message from an unknown number or call the number. Block the number outright if you can. Even if the text message says “text ‘stop’ to stop receiving messages,” never reply. Providing a response to the message will verify to them that the number is active.
- Do a web search of both the number and the message content. If the phishing message appears to be impersonating a company, call the company directly at the number on their official site to confirm the message’s authenticity.