On May 23rd, another Elasticsearch misconfiguration incident has led to the exposure of the personal details and Aadhar number for millions of families registered under Mukhya Mantri Parivar Samridhi Yojana (MMPSY), which is one of the largest social security programme in India rolled out in the state of Haryana.
IP in question was first indexed by BinaryEdge search engine on May 21st. I have immediately sent numerous email alerts to the potential administrators of the database and within 24 hours the instance was taken down from public domain.
Thank you for flagging the issue.
It has been duly noted.
It is unknown if anybody else found this server, but chances are high given the growing numbers of attacks on unprotected noSQL databases registered for the last year.
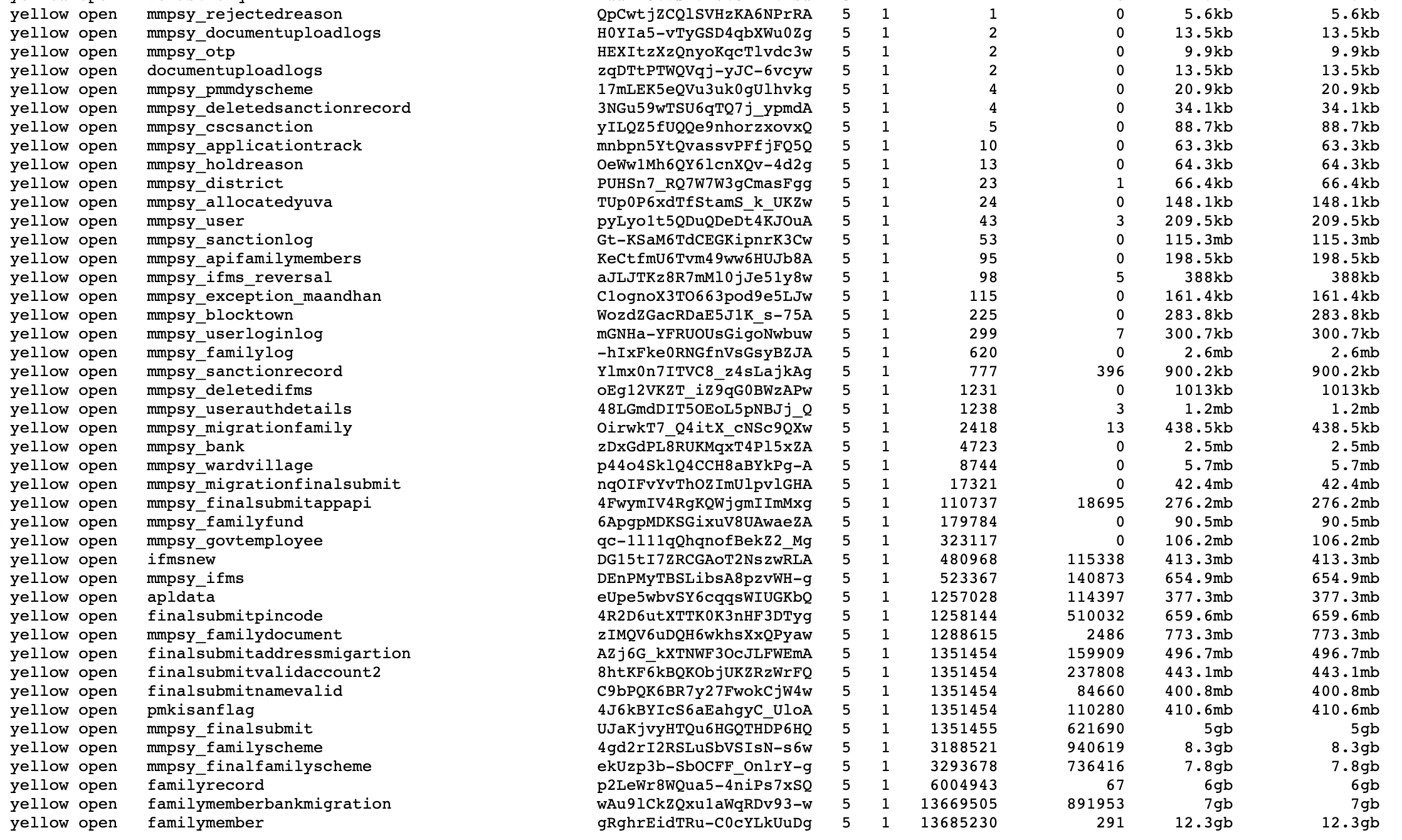
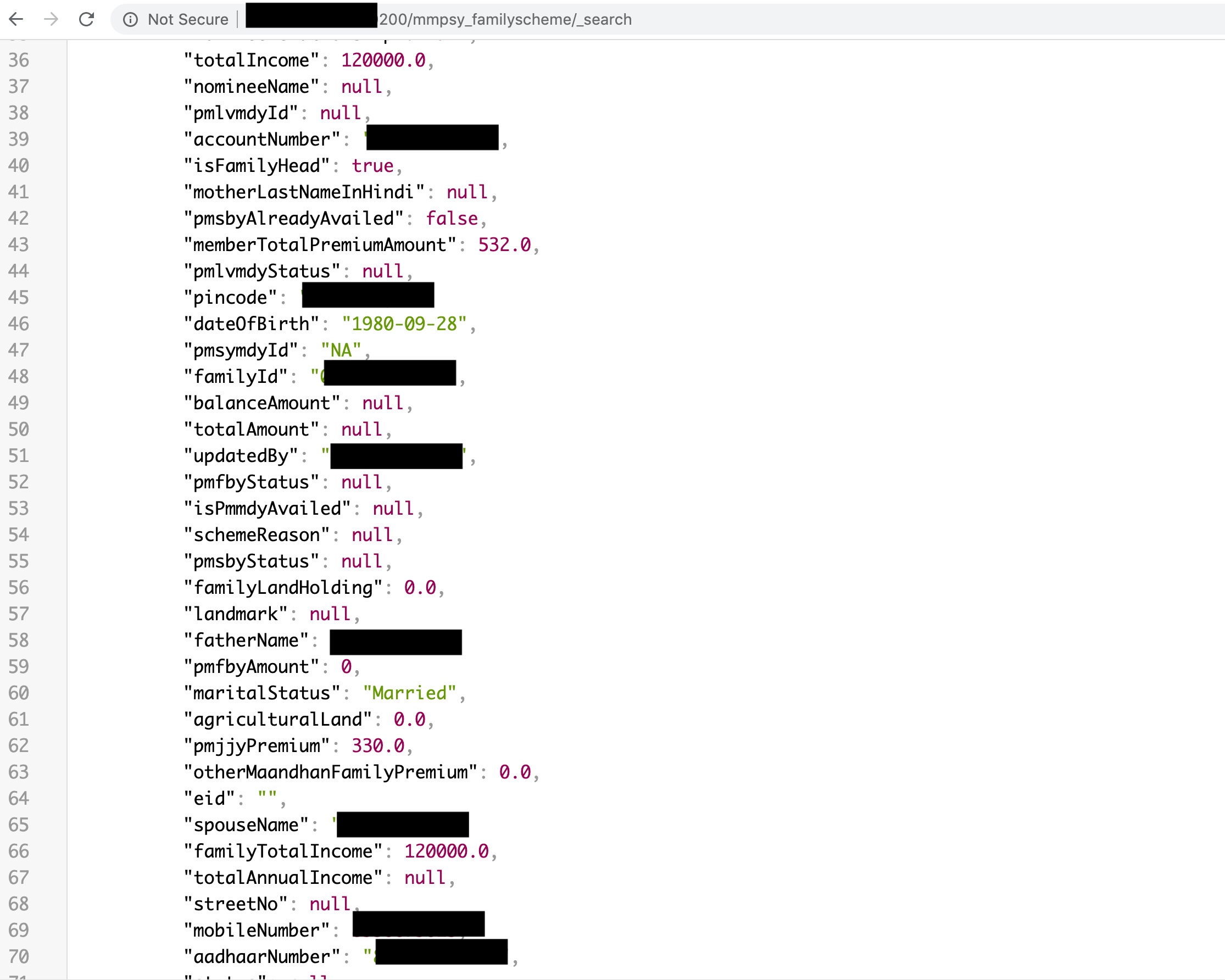
Among exposed data the following was visible:
- full name
- address
- mobile phone number
- marital status
- mother’s name
- spouse name
- gender
- date of birth, age
- Aadhar number
- income details and many more.
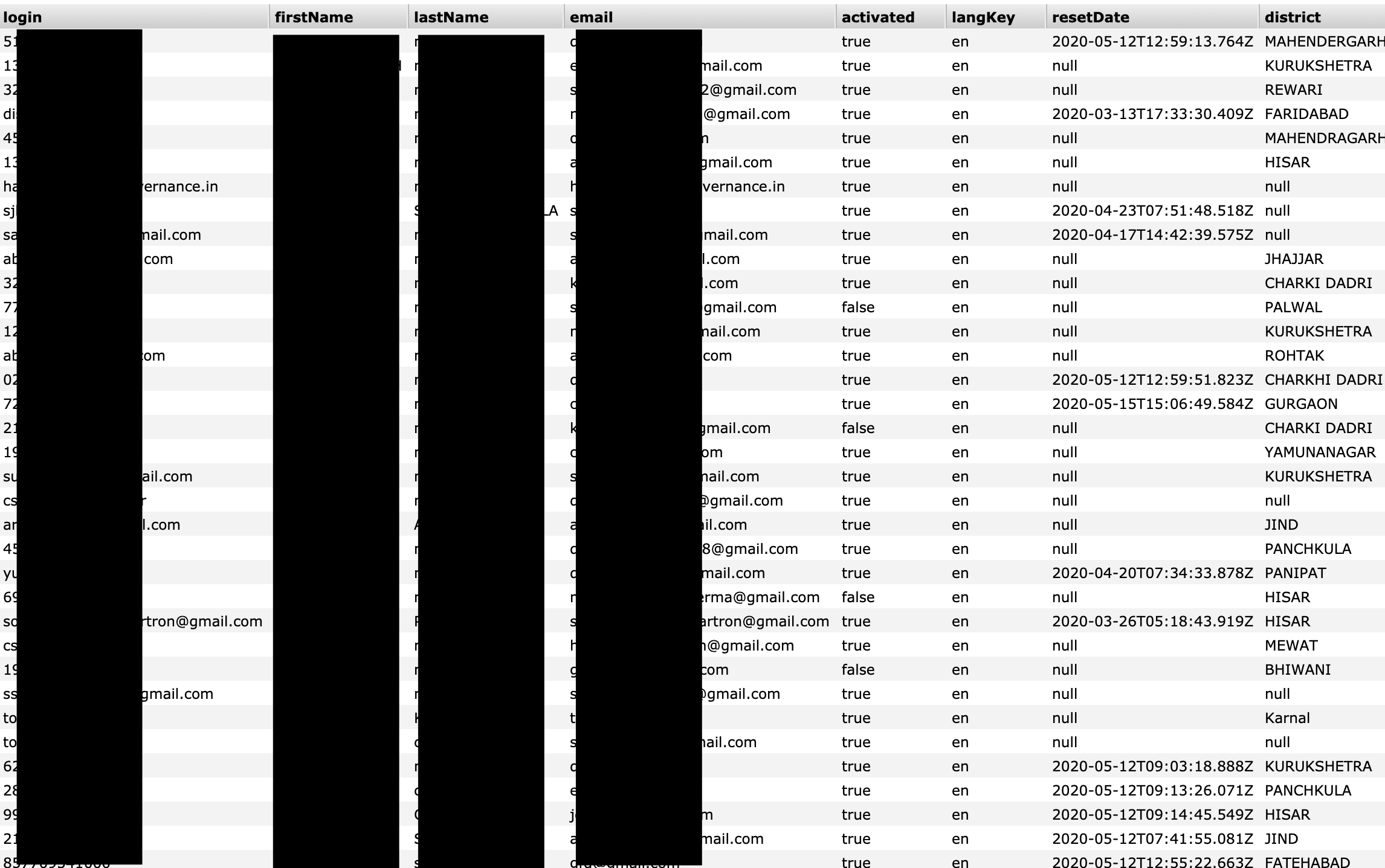
Additionally, database contained login and authentication tokens for administration purposes.
Dangers of exposed data
Such structured and targeted collection of data would pose a clear risk to people whose data was exposed. An identity thief or phishing actor couldn’t ask for a better payload.
Fraudsters might target affected people with scams and phishing campaigns, using their personal information to craft targeted messages
Phishing messages often impersonate trusted people or organizations to trick victims into giving up sensitive information or money. They often contain links to phishing websites, which mimic genuine websites. In fact, they exist only to steal information, such as passwords and payment information.
How and why we discovered this exposure
Our goal is to help to protect data on the Internet by identifying data leaks and following responsible disclosure policies. Our mission is to make the cyber world safer by educating businesses and communities worldwide.
Our extensive cybersecurity knowledge lends itself well to searching for and analyzing data leaks. Our due diligence demands that we make every attempt to identify who is responsible and notify them as quickly as possible.
Our hope is to minimize harm to end users whose data was exposed. We take steps to find out what each database contained, for how long it was exposed, and what threats to end users might arise as a result. Our findings are compiled into reports like this one to raise awareness and curb misuse of personal data by malicious parties.