On August 14th I have sent a responsible disclosure notice to Gartner, the world’s leading information technology research and advisory company, alerting them on a misconfigured Elasticsearch cluster with 1TB+ of data.
According to Shodan and BinaryEdge search engines, database was set to public since January and apparently had affiliation with CEB Inc., the industry leader in providing best practice and talent management insights. Gartner has completed its acquisition of CEB in April 2017.
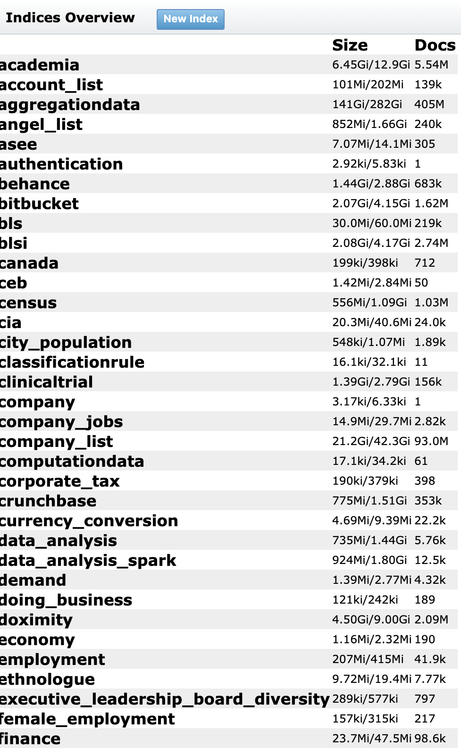
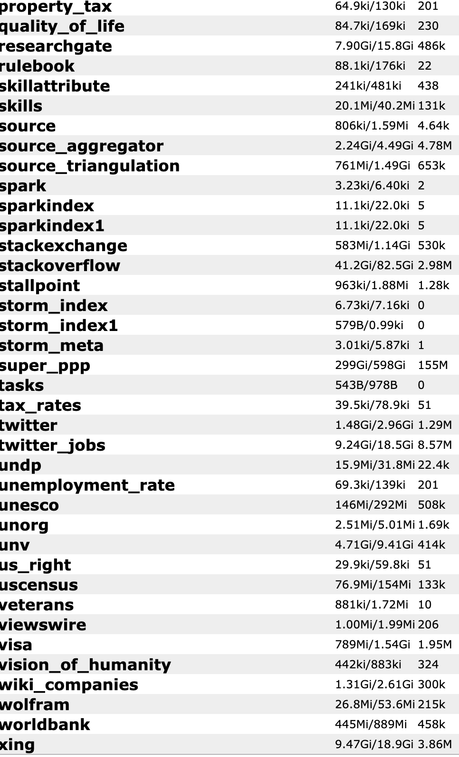
Database in question contained the following collections:
In a response to my notification email, Gartner thanked me for the responsible disclosure, immediately secured the database and claimed that all data was collected from public sources.
Thanks again for bringing this to our attention. We’ve investigated the issue and can confirm this was a legacy system containing only publicly sourced data. We have taken steps to remove public access to the system.
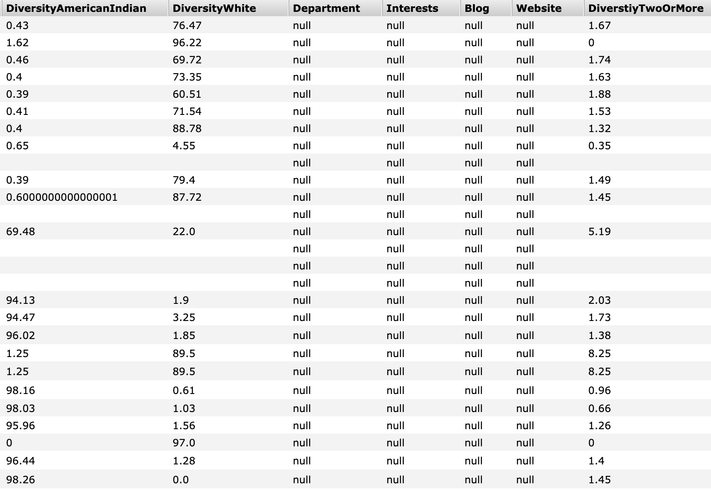
However, at least one collection from database named “super_ppp” contained more than 155M of records with quite detailed personal information, name, bio, skills, employment collected from LinkedIn / Github (with Github records containing emails as well), plus such fields as “Diversity”:
Additionally, an API key was also part of the exposure and could have been used to access even more information.
From my experience, even publicly sourced data collected in one place is still a treasure trove for malicious actors who might use this data to cross-reference with other breaches and come up with a full profile on a person and use it in phishing.
It is unknown, whether somebody else has accessed the data while it was set to public but the chances are high that this information had been exfiltrated at some point.
Danger of having exposed Elasticsearch or similar NoSql databases is huge. I have previously reported that the lack of authentication allowed the installation of malware or ransomware on the Elasticsearch servers. The public configuration allows the possibility of cybercriminals to manage the whole system with full administrative privileges. Once the malware is in place criminals could remotely access the server resources and even launch a code execution to steal or completely destroy any saved data the server contains.
***
As we see a never-ending loop of these incidents, we at SecurityDiscovery.com have decided to offer a live educational session (webinar or offline workshop) for raising cyber security awareness within your organization, to prevent potential issues in the future. We use real world examples and promote that data security is important to every employee and at every level inside the organization.
It can be an online webinar session (estimated 1h long), with Q&A session or an offline meeting in your offices, live interaction with your team (master class included).
Proposed content includes:
- Description of tools and techniques we use to identify vulnerabilities, PII and sensitive data online: no hacking, just google-it.
- How to ensure your data / your company’s data is not exposed to the public internet, security tips from professionals
- Recommendations and best practice on main noSQL databases configurations and maintenance (MongoDB, CouchDB, Elasticsearch)
- Case studies: analyzing related data appearance online
- Live search for data and master class
Please feel free to send your requests to alert(at)securitydiscovery.com or bob(at)securitydiscovery.com
Let’s educate your team!