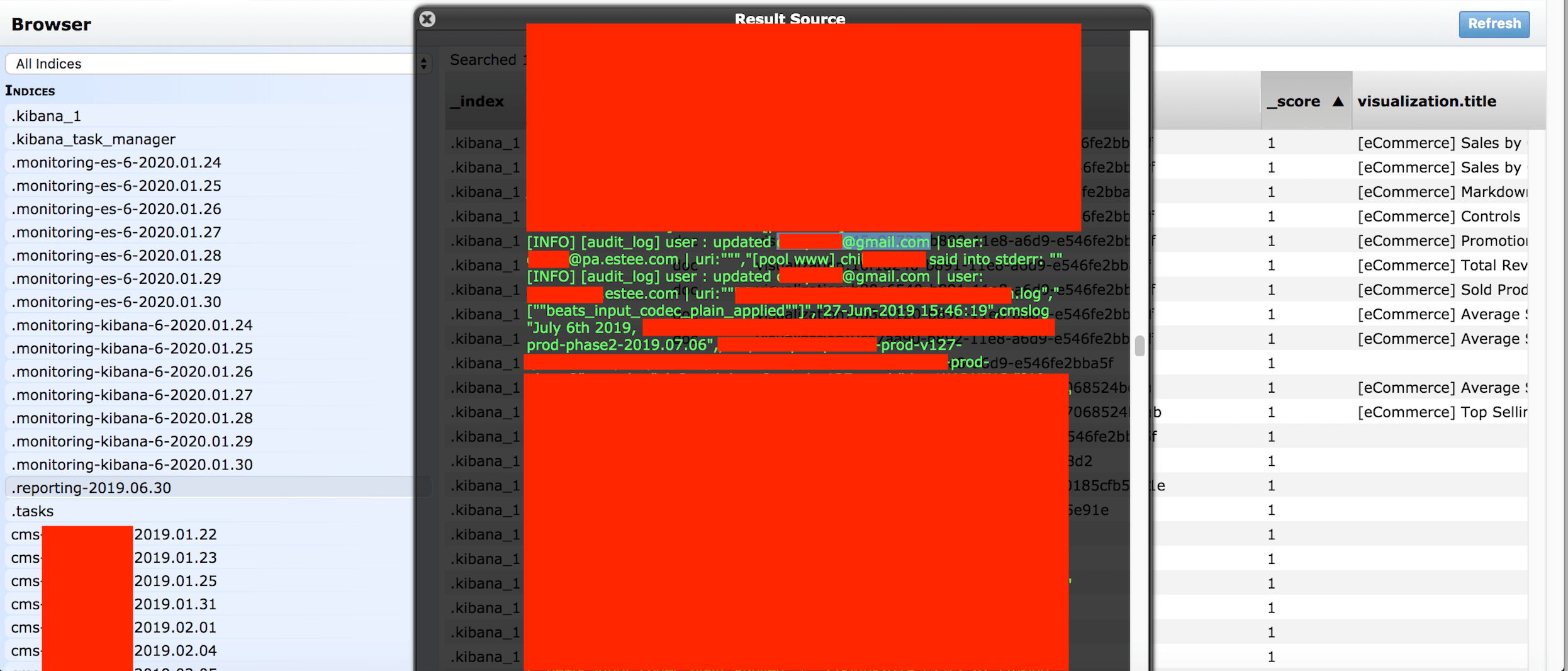
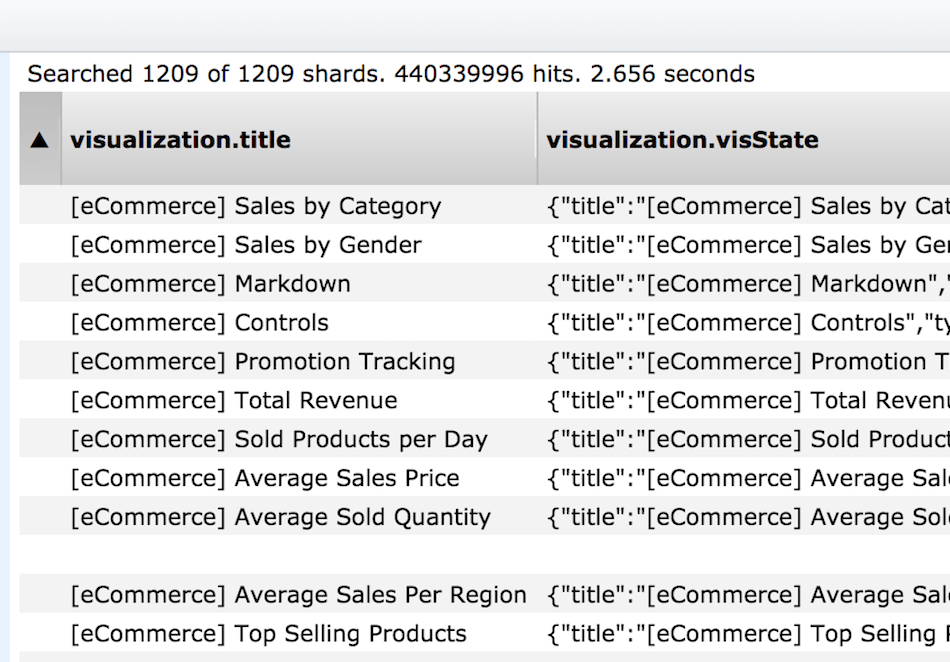
On January 30th I discovered a non-password protected database that contained a massive amount of records totaling 440,336,852. Upon further review I was able to see connections to New York based cosmetic company Estée Lauder. I could see audit logs that contained a large number of email addresses in each document. I immediately sent a responsible disclosure notice Estée Lauder alerting them to the exposure.
As in most large companies when reporting a data exposure it is usually extremely difficult to get through the firewall of gate-keepes, but several hours later and multiple emails the data was still exposed. After calling every phone number I could find I was able to reach someone by phone who then promised to pass on the information. The company acted fast and professionally and restricted public access to the database on the same day as my notification.
This company has been a household name for over 70 years and had an annual revenue of $14.863B in 2019 it seems logical that there would be a large dataset associated with the business. According to Wikipedia “ESTĒE LAUDER is an American multinational manufacturer and marketer of prestige skincare, makeup, fragrance and hair care products, based in Midtown Manhattan, New York City. The company owns a diverse portfolio of brands, distributed internationally through both digital commerce and retail channels”. I can only speculate or assume that the email addresses were from digital commerce or online sales.
Here is what we discovered:
- 440,336,852 logs and records that should not have been publicly exposed online.
- “User” emails in plain text (including internal email addresses from the @estee.com domain)
- Production, Audit, Error, CMS, and Middleware logs were exposed.
- References to reports and other internal documents.
- IP addresses, Ports, Pathways, and storage info that cyber criminals could exploit to access deeper into the network.
There were millions of records pertaining to middleware that is used by the Estée Lauder company. Middleware is software that provides common services and capabilities to applications outside of what’s offered by the operating system.
In 2011 databreaches.net reported Estée Lauder sent a notice regarding the theft of a company-issued laptop that contained names and Social Security Numbers of current and former employees and contractors for the firm. In the internal memo it appears the company requested users to change their passwords and use encryption.
To the best of my knowledge the database did not contain payment data or sensitive employee information based on what I personally saw. I reported my findings as soon as I made an assumption of who owned the data and did not have the time to validate 440 million records before public access was closed. With the understanding that every second counts when it comes to the risks of a data exposure our top priority was alerting Estée Lauder.
It is unclear exactly how many “user” email addresses were exposed. It is also unclear how long the Estée Lauder database was exposed or who else may have accessed the records. As security researchers our primary goal is data protection and when we see consumer data of any kind the first priority is to alert the owner to take immediate action. Our mission is to highlight data protection and raise awareness that companies and organizations must do more to protect the data they collect and store. We follow a responsible disclosure process and securely delete any screenshots or information taken for verification purposes. Estée Lauder did not provide a statement for this story but was responsive in communicating that they had received the notice, thanked us for alerting them, and had completed their internal investigation.
For more on this story see the coverage in Forbes.
About Us: Security Discovery helps organizations identify and mitigate risks through news, education, and cyber security services. Our clients range from startups to Fortune 100 companies and our readers are global. We advise our clients to never rely on a single security provider for your data protection and diversify your penetration testing providers. Having an official scope in place for a Bug Bounty program to invite legitimate members of the security community to identify vulnerabilities is also not a bad idea. When it comes to cyber security never put all of your eggs in one basket and the more eyes on your network, the better. For questions or information please contact me: [email protected].