Bold.com, company behind popular solutions to help jobseekers find jobs, and help businesses find candidates – LiveCareer, Resume-Now, my Perfect Resume, Mighty Recruiter – inadvertently exposed part of its internal infrastructure used for project tracking and project management.
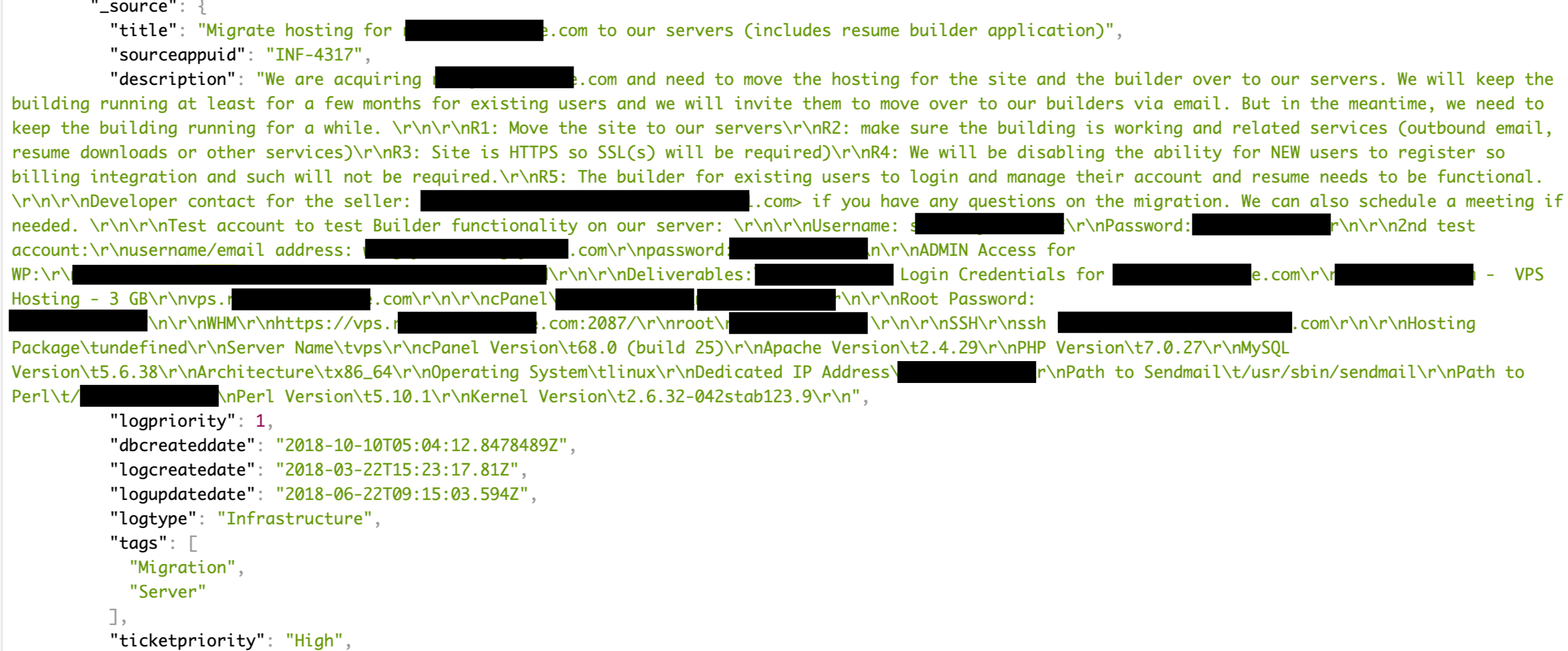
On August 10, I have identified an unprotected Elasticsearch cluster with thousands of records containing sensitive information not intended for public view which appeared to belong to Bold.com infrastructure team. Some tickets described migration processes to new servers with full access details and privileges preferences, while other collections included information on catalogues structure and databases and admin logins.
I have immediately notified administrators as part of our responsible disclosure protocol and received confirmation from one of the managers that “we are looking into it”. On the same day public access to an open Elasticsearch was restricted.
According to Shodan historical data for this IP Elasticsearch port (9200) was first indexed in December 2018. Additionally, Kibana interface was also set open since August last year.
It is unknown whether somebody else have accessed database while it was open, but it appears that at least one of the Bold.com’s service instances (Jenkins for LiveCareer.com) was targeted by GandCrab v.5.2 ransomware (good news – there is a decryptor for this version available).
Danger of having exposed Elasticsearch or similar NoSql databases is huge. I have previously reported that the lack of authentication allowed the installation of malware or ransomware on the Elasticsearch servers. The public configuration allows the possibility of cybercriminals to manage the whole system with full administrative privileges. Once the malware is in place criminals could remotely access the server resources and even launch a code execution to steal or completely destroy any saved data the server contains.
***
As we see a never-ending loop of these incidents, we at SecurityDiscovery.com have decided to offer a live educational session (webinar or offline workshop) for raising cyber security awareness within your organization, to prevent potential issues in the future. We use real world examples and promote that data security is important to every employee and at every level inside the organization.
It can be an online webinar session (estimated 1h long), with Q&A session or an offline meeting in your offices, live interaction with your team (master class included).
Proposed content includes:
- Description of tools and techniques we use to identify vulnerabilities, PII and sensitive data online: no hacking, just google-it.
- How to ensure your data / your company’s data is not exposed to the public internet, security tips from professionals
- Recommendations and best practice on main noSQL databases configurations and maintenance (MongoDB, CouchDB, Elasticsearch)
- Case studies: analyzing related data appearance online
- Live search for data and master class
Please feel free to send your requests to alert(at)securitydiscovery.com or bob(at)securitydiscovery.com
Let’s educate your team!