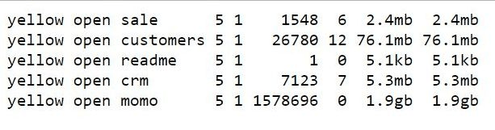
On Nov 29th 2018 I have identified an unprotected Elasticsearch cluster, available for public access, via Shodan engine.
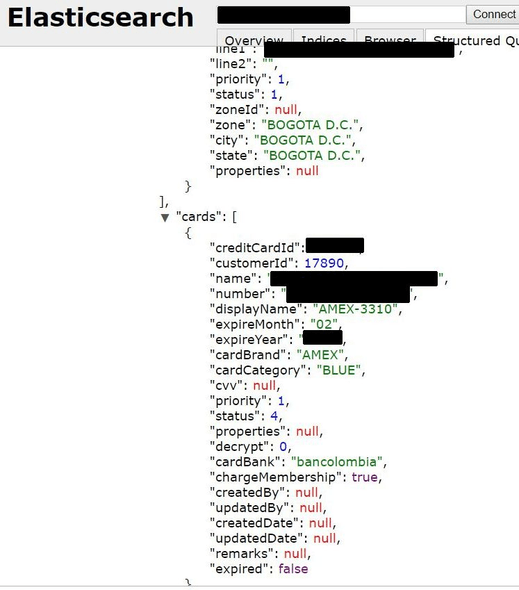
It took me some time before I analyzed the data and noted that almost all payment information (credit cards details) was related to Bancolombia, so I decided it would be the quickest possible solution to prevent this data from being stolen and report the incident directly to bank authorities.
Shortly after I contacted Bancolombia, instance has been secured (Nov.30) and on the next day I was contacted by a representative of a company that managed the data, Waumovil, who thanked me for the heads up and said that “unfortunately we had some open ports that I was not aware“. Data appeared to be part of their CRM system.
Later on, some of my Colombia-based Twitter followers confirmed that Bancolombia reached out to them and informed on the incident.
We have previously reported that the lack of authentication allowed the installation of malware or ransomware on the Elasticsearch servers. The public configuration allows the possibility of cybercriminals to manage the entire system with full administrative privileges. Once the malware is in place criminals could remotely access the server resources and even launch a code execution to steal or completely destroy any saved data the server contains.
Although company reacted fast to secure their data it is unclear how long it may have been publicly available or who else might have accessed the files. Data privacy and data protection laws like GDPR are a good first step but companies and charities need to be proactive when it comes to data protection.
About author:
Bob Diachenko has over 12 years experience working in corporate/product/internal communications with a strong focus on infosecurity, IT and technology. In the past Bob has worked with top tier media, government agencies, and law enforcement to help secure exposed data. Follow Bob on Twitter and his blog on Linkedin, email: [email protected]