On January 11th, Bob Diachenko of SecurityDiscovery.com, identified another unprotected Elasticsearch instance which contained millions of records – this time related to AIESEC, “the world’s largest youth-run organization. According to Wikipedia the AIESEC network has 27,500 leadership positions and over 100,000 members in 127 countries.
The IP with the exposed database has been indexed by Shodan and other public search engines which are specialized in Internet-of-Things (IoT).
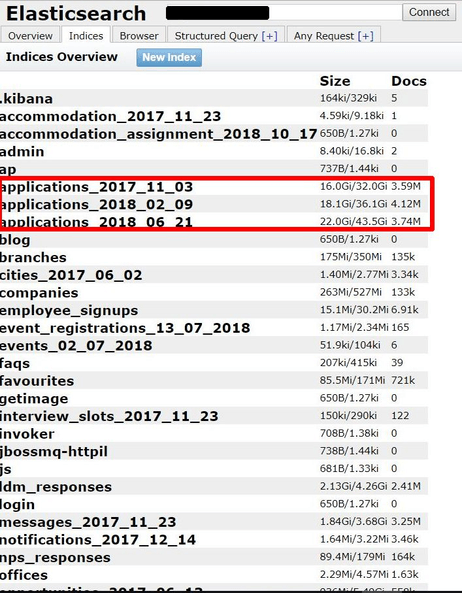
Elasticsearch cluster in question had the following indexes:
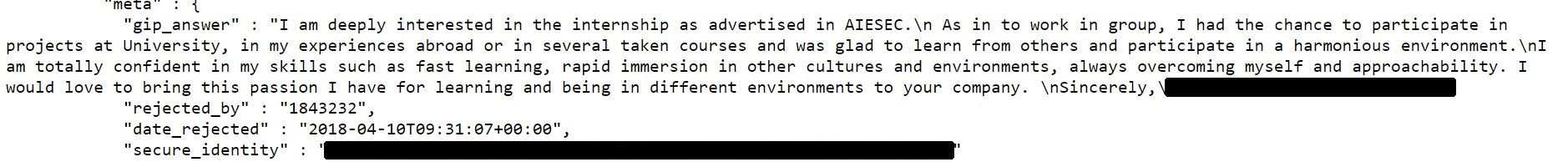
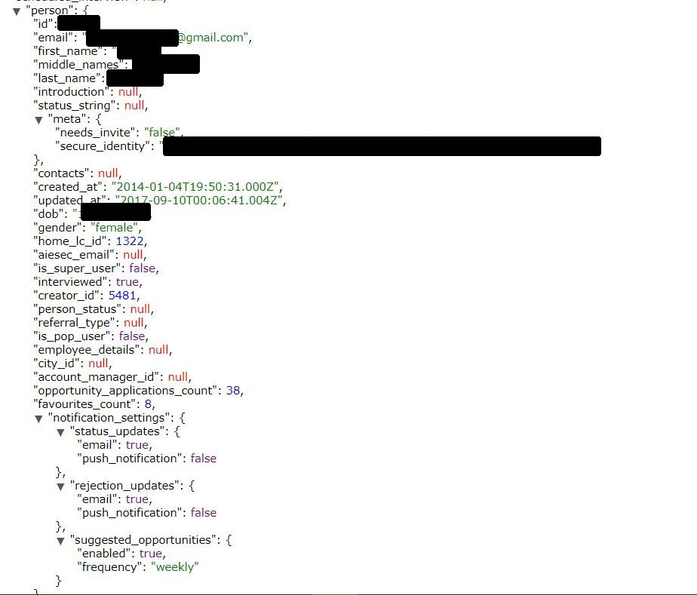
Among other information, the database contained around 4 million of applications which were tagged as “opportunity applications” for AIESEC internships and included sensitive information as email, full name, DOB, gender, plus a detailed description on their intentions for applying for AIESEC as well as interview details:
Breach Notification and Response
On Jan 11th, Bob Diachenko contacted AIESEC through several different communication channels and luckily his notification reached the right people in the organization and the exposed cluster was quickly secured.
The following statements have been made by AIESEC regarding the data leak:
“We take the security of our customers information extremely seriously. After looking into this matter, we immediately secured the vulnerability, disabling unauthorized access to the cluster. The data was cached on the node for testing purposes and mistakenly left unsecured. We can confirm that the server now contains no sensitive information. That said, we’ll use this event for our own awareness for our development team and are now checking our system for further similar vulnerabilities. We do very much appreciate your letting us know of this issue and your dedication to keeping the web secure”
According to AIESEC spokesperson:
“The vulnerability arose from a misconfiguration that was introduced into the Elasticsearch servers while evaluating certain improvements for the cluster as part of a current infrastructure improvement project we are running. We started work around 20 days ago [prior to Jan 11th, when notification was sent. – Bob Diachenko’s note], so this is around when the misconfiguration was introduced”. We have already contacted the data protection authorities and the affected users as per GDPR protocol”.
The Danger of Leaving the Front Door Open
We have previously reported that the lack of authentication allowed the installation of malware or ransomware on the Elasticsearch servers. The public configuration allows the possibility of cybercriminals to manage the entire system with full administrative privileges. Once the malware is in place criminals could remotely access the server resources and even launch a code execution to steal or completely destroy any saved data the server contains.
Although AIESEC acted fast to secure their data it is unclear how long it may have been publicly available or who else might have accessed the millions of files containing PII. This raises the question of how charities and non-profits with limited resources can afford to safely manage millions of sensitive files? Data privacy and data protection laws like GDPR are a good first step but companies and charities need to be proactive when it comes to data protection. In 2017 a government study in the UK concluded that nine in ten businesses and charities had done nothing or very little to prepare or comply with the European Union’s General Data Protection Regulation. This case yet again highlights just how important cyber security is among charities.
About author:
Bob Diachenko has over 12 years experience working in corporate/product/internal communications with a strong focus on infosecurity, IT and technology. In the past Bob has worked with top tier media, government agencies, and law enforcement to help secure exposed data. Follow Bob on Twitter and his blog on Linkedin, email: [email protected]